Countdown to Live Session
00
Days
00
Hours
00
Minutes
00
Seconds
Key Discussion Points
Why Indian Websites Are Targeted
Common attack vectors targeting Indian web apps and APIs, why traffic spikes often mask active threats, and what makes the Indian internet a high-value target for bad actors.
The Security Gap Most Teams Miss
Where hosting-level protection ends and application-layer exposure begins. The misconfigurations that leave you vulnerable even when a firewall is running.
Security Layers, Simply Explained
What WAF rules actually block, how DDoS mitigation work, where bot filtering kicks in, and why all three need to work together for APIs and dynamic applications to stay protected under real-world load.
Live Q&A With Experts
10 minutes of live Q&A answered by our experts. Bring your real questions on WAF, DDoS attacks, bot attacks. We will help you think it through with practical next steps.
Meet our Speaker
Arsath has spent 5+ years working across the full spectrum of application security. WAF, DDoS, bot protection, and beyond. At VergeCloud, he turns security complexity into clarity, helping teams build defenses that work under real-world conditions.
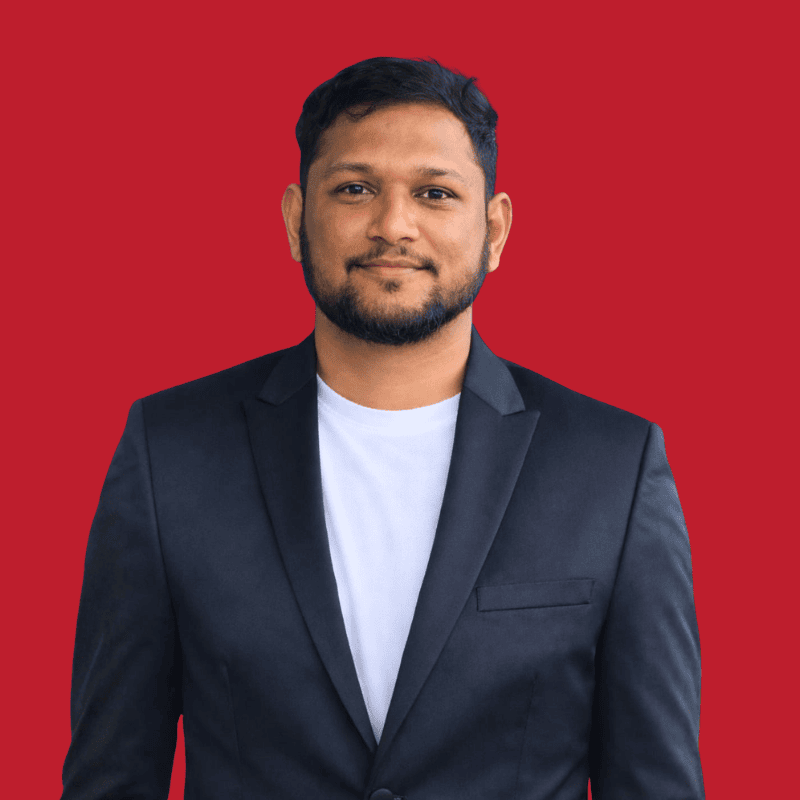
Arsath Parves
Solution Engineer
This webinar is best suited for
IT Heads, DevOps Leaders, Product Owners & Solution Architects
Startups & Enterprises with customer-facing websites, portals, or APIs
Technology Leaders evaluating or scaling their application security posture
Students, Interns & Early-Career Engineers learning web security fundamentals
Students, Interns & Early-Career Engineers learning web security fundamentals
What You’ll Take Away From This Session
Understand the Real Threat Landscape
See what attack types actively target Indian websites and APIs, and why standard hosting-level protection is rarely enough.
Know What Your Security Stack Is and Is Not Doing
Understand the difference between WAF, DDoS mitigation, bot filtering, and firewall layers and where the gaps usually are.
Build Practical Security and Response Patterns
Learn how to configure rules, set thresholds, and respond to incidents without breaking your application or triggering false positives.
Operate Security Like a Production Team
Get a clear view of security governance basics: logging, alerting, rate limiting, and incident escalation workflows.
